The important thing advantage of Battering RAM is that it requires gear that prices lower than $50 to tug off. It additionally permits energetic decryption, which means encrypted knowledge will be each learn and tampered with. As well as, it really works towards each SGX and SEV-SNP, so long as they work with DDR4 reminiscence modules.
Wiretap
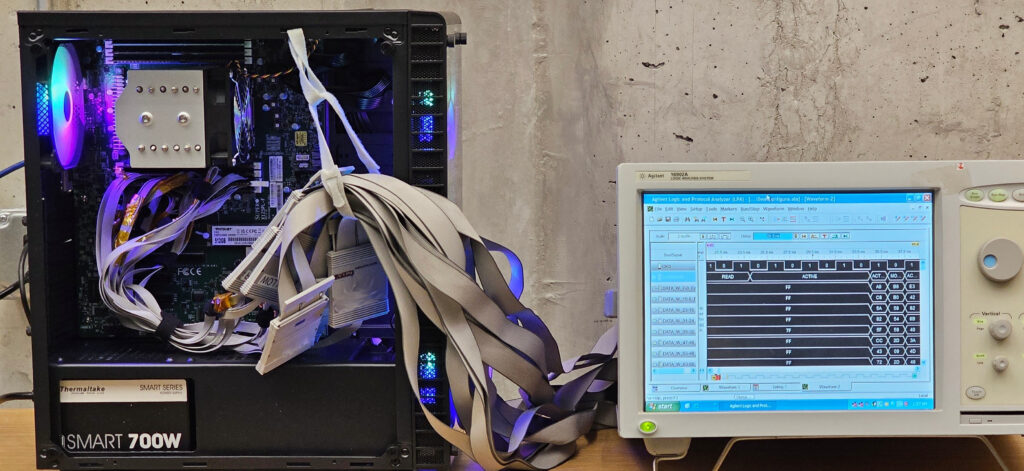
Wiretap, in the meantime, is restricted to breaking solely SGX working with DDR4, though the researchers say it will seemingly work towards the AMD protections with a modest quantity of further work. Wiretap, nevertheless, permits just for passive decryption, which implies protected knowledge will be learn, however knowledge can’t be written to protected areas of reminiscence. The price of the interposer and the gear for analyzing the captured knowledge additionally prices significantly greater than Battering RAM, at about $500 to $1,000.
The Wiretap interposer.
Credit score:
Seto, et al.
The Wiretap interposer related to a logic analyzer.
Credit score:
Seto, et al.
Like Battering RAM, Wiretap exploits deterministic encryption, besides the latter assault maps ciphertext to an inventory of identified plaintext phrases that the ciphertext is derived from. Ultimately, the assault can recuperate sufficient ciphertext to reconstruct the attestation key.
Genkin defined:
Let’s say you could have an encrypted record of phrases that will likely be later used to kind sentences. You realize the record upfront, and also you get an encrypted record in the identical order (therefore you recognize the mapping between every phrase and its corresponding encryption). Then, if you encounter an encrypted sentence, you simply take the encryption of every phrase and match it towards your record. By going phrase by phrase, you possibly can decrypt the complete sentence. In truth, so long as a lot of the phrases are in your record, you possibly can most likely decrypt the complete dialog ultimately. In our case, we construct a dictionary between frequent values occurring throughout the ECDSA algorithm and their corresponding encryption, after which use this dictionary to recuperate these values as they seem, permitting us to extract the important thing.
The Wiretap researchers went on to point out the kinds of assaults which are potential when an adversary efficiently compromises SGX safety. As Intel explains, a key advantage of SGX is distant attestation, a course of that first verifies the authenticity and integrity of VMs or different software program working contained in the enclave and hasn’t been tampered with. As soon as the software program passes inspection, the enclave sends the distant social gathering a digitally signed certificates offering the identification of the examined software program and a clear invoice of well being certifying the software program is secure.