“One of the crucial uncommon parts of this case was the attacker’s use of bodily entry to put in a Raspberry Pi machine,” Group-IB Senior Digital Forensics and Incident Response Specialist Nam Le Phuong wrote. “This machine was related on to the identical community change because the ATM, successfully inserting it contained in the financial institution’s inside community. The Raspberry Pi was outfitted with a 4G modem, permitting distant entry over cell information.”
To keep up persistence, UNC2891 additionally compromised a mail server as a result of it had fixed Web connectivity. The Raspberry Pi and the mail server backdoor would then talk by utilizing the financial institution’s monitoring server as an middleman. The monitoring server was chosen as a result of it had entry to virtually each server throughout the information heart.
The Community Monitoring Server as an middleman between the Raspberry Pi and the Mail Server.
Credit score:
Group-IB
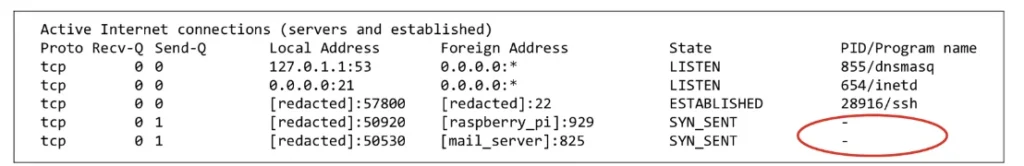
As Group-IB was initially investigating the financial institution’s community, researchers seen some uncommon behaviors on the monitoring server, together with an outbound beaconing sign each 10 minutes and repeated connection makes an attempt to an unknown machine. The researchers then used a forensic instrument to research the communications. The instrument recognized the endpoints as a Raspberry Pi and the mail server however was unable to determine the method names chargeable for the beaconing.
The forensic triage instrument is unable to gather the related course of identify or ID related to the socket.
Credit score:
Group-IB
The researchers then captured the system reminiscence because the beacons had been despatched. The overview recognized the method as lightdm, a course of related to an open supply LightDM show supervisor. The method seemed to be reliable, however the researchers discovered it suspicious as a result of the LightDM binary was put in in an uncommon location. After additional investigation, the researchers found that the processes of the customized backdoor had been intentionally disguised in an try and throw researchers off the scent.
Phuong defined:
The backdoor course of is intentionally obfuscated by the menace actor by using course of masquerading. Particularly, the binary is called “lightdm”, mimicking the reliable LightDM show supervisor generally discovered on Linux methods. To reinforce the deception, the method is executed with command-line arguments resembling reliable parameters – for instance,
lightdm –session youngster 11 19 — in an effort to evade detection and mislead forensic analysts throughout post-compromise investigations.
These backdoors had been actively establishing connections to each the Raspberry Pi and the interior Mail Server.
As famous earlier, the processes had been disguised utilizing the Linux bind mount. Following that discovery, Group-IB added the method to the MITRE ATT&CK framework as “T1564.013 – Conceal Artifacts: Bind Mounts.”
Group-IB didn’t say the place the compromised switching tools was positioned or how attackers managed to plant the Raspberry Pi. The assault was detected and shut down earlier than UNC2891 was in a position to obtain its closing aim of infecting the ATM switching community with the CakeTap backdoor.