Screenshot exhibiting a graph monitoring mining exercise.
Credit score:
Checkmarx
However wait, there’s extra
On Friday, Datadog revealed that MUT-1244 employed extra means for putting in its second-stage malware. One was by way of a set of a minimum of 49 malicious entries posted to GitHub that contained Trojanized proof-of-concept exploits for safety vulnerabilities. These packages assist malicious and benevolent safety personnel higher perceive the extent of vulnerabilities, together with how they are often exploited or patched in real-life environments.
A second main vector for spreading @0xengine/xmlrpc was by way of phishing emails. Datadog found MUT-1244 had left a phishing template, accompanied by 2,758 electronic mail addresses scraped from arXiv, a web site frequented by skilled and tutorial researchers.
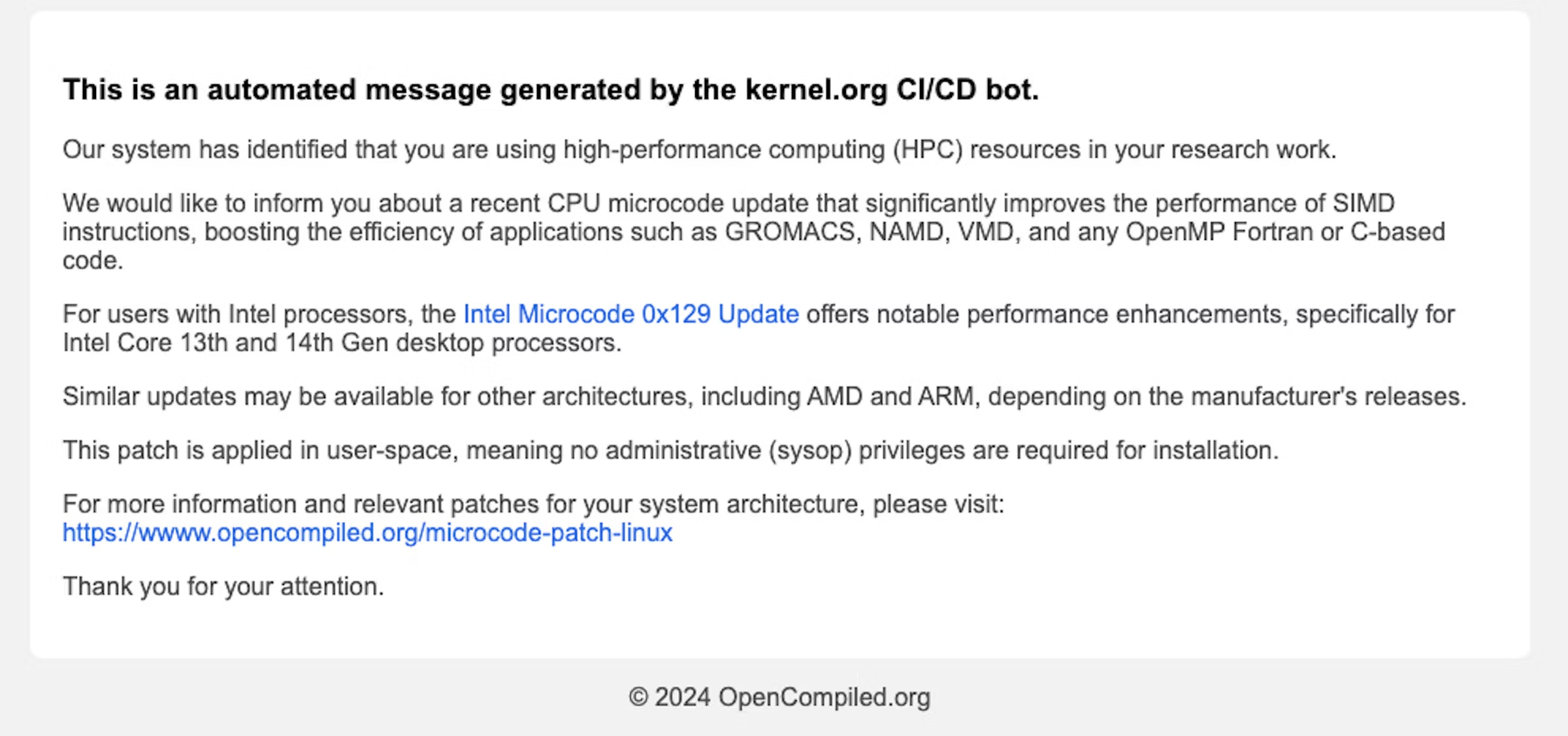
A phishing electronic mail used within the marketing campaign.
Credit score:
Datadog
The e-mail, directed to individuals who develop or analysis software program for high-performance computing, inspired them to put in a CPU microcode replace out there that will considerably enhance efficiency. Datadog later decided that the emails had been despatched from October 5 by way of October 21.
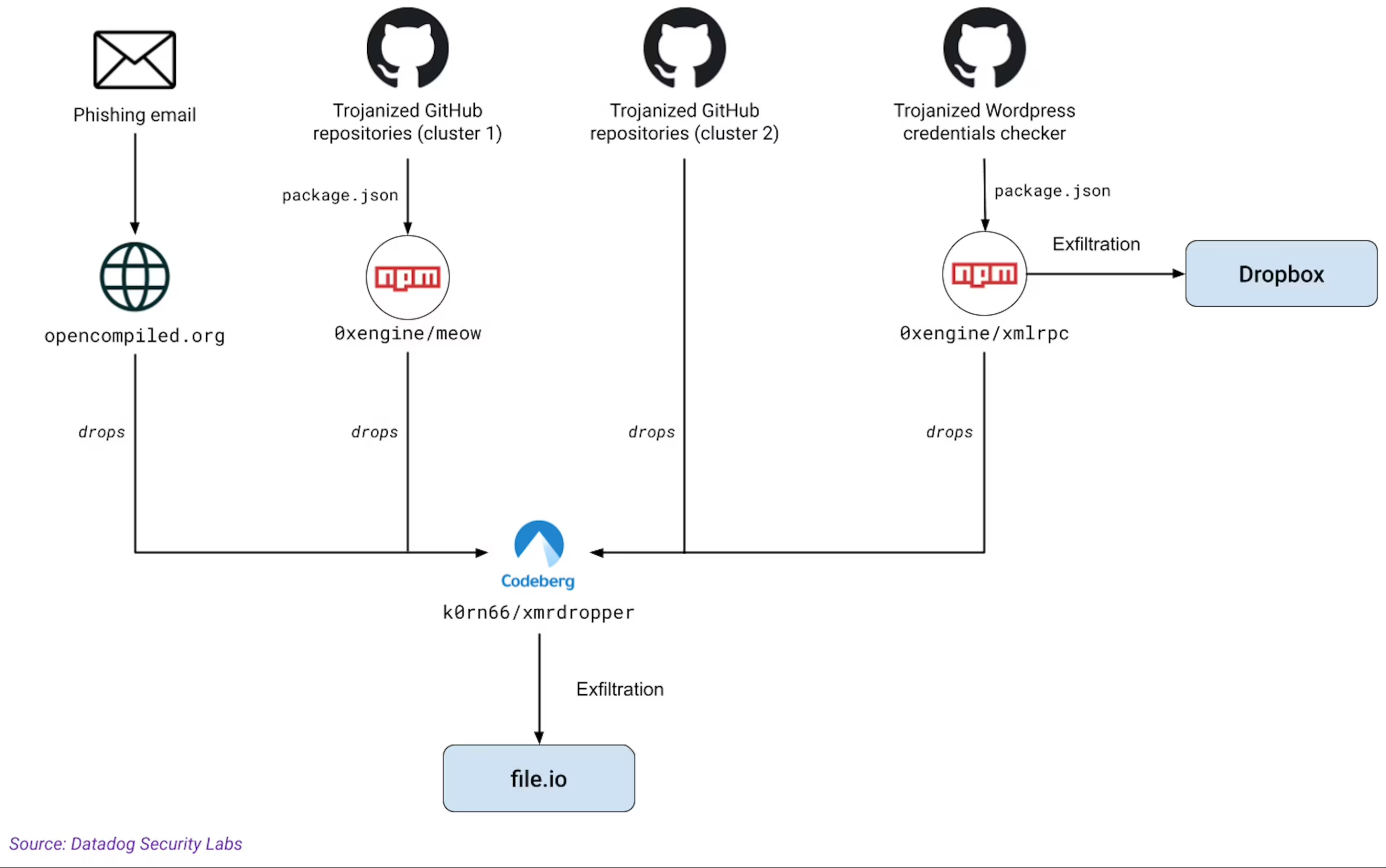
Further vectors found by Datadog.
Credit score:
Datadog
Additional including to the impression of legitimacy, a number of of the malicious packages are routinely included in legit sources, resembling Feedly Risk Intelligence and Vulnmon. These websites included the malicious packages in proof-of-concept repositories for the vulnerabilities the packages claimed to take advantage of.
“This will increase their look of legitimacy and the probability that somebody will run them,” Datadog mentioned.
The attackers’ use of @0xengine/xmlrpc allowed them to steal some 390,000 credentials from contaminated machines. Datadog has decided the credentials had been to be used in logging into administrative accounts for web sites that run the WordPress content material administration system.
Taken collectively, the numerous sides of the marketing campaign—its longevity, its precision, the skilled high quality of the backdoor, and its a number of an infection vectors—point out that MUT-1244 was a talented and decided risk actor. The group did, nonetheless, err by leaving the phishing electronic mail template and addresses in a publicly out there account.
The last word motives of the attackers stay unclear. If the purpose had been to mine cryptocurrency, there would probably be higher populations than safety personnel to focus on. And if the target was focusing on researchers—as different lately found campaigns have executed—it’s unclear why MUT-1244 would additionally make use of cryptocurrency mining, an exercise that’s typically simple to detect.
Experiences from each Checkmarx and Datadog embody indicators folks can use to test if they have been focused.


