reside by a paradigm shift in how we show we’re who we are saying we’re on-line. As an alternative of asking What have you learnt? (password, PIN, mom’s maiden title) or What do you appear to be? (Face ID, fingerprint) the query has turn into How do you behave?
Generative AI and developments in malware expertise similar to RATs (Distant Entry Trojans) have enabled cybercriminals to scale assaults and even bypass safety measures like Face ID or MFA, as soon as thought-about bulletproof.
Behavioral biometrics evaluation is now changing into customary apply at banks, that are chargeable for protecting losses from cybercrimes until the safety measures they put in place meet the challenges of those new assault surfaces.
Computational Motor Management Idea
Once you scroll by a dropdown menu or drag a slider in your cellphone, your mind is executing an intricate suggestions loop, correcting imperceptible errors within the path as you journey every unconscious millimeter and millisecond of the gesture.
In its infancy, behavioral biometrics sought to distinguish human conduct from bot conduct. Researchers quickly found that the identical expertise may be utilized to distinguishing one human’s conduct from the conduct of one other human.
Computational motor management principle, a multidisciplinary area that mixes neuroscience with biomechanics and laptop science, supplies researchers with the framework for understanding essentially the most discriminating options of human conduct.
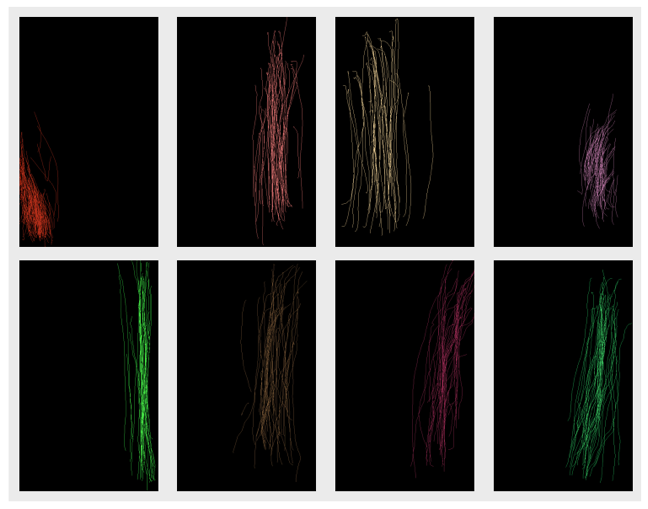
Analysis reveals that what we consider as “robotic” – these unconscious neural corrections – are literally what make an individual’s behavioral profile so not possible to recreate. A 2012 examine on the College of California at Berkeley known as Touchalytics, which analyzed scroll patterns throughout 41 members as they sifted by textual content and pictures on their smartphones, proved that after solely 11 scroll strokes behavioral fashions may establish a selected person from the group with out error.
Digital Tells
The Berkeley examine identifies 30 behavioral options distinctive to every person’s scrolling habits, together with stroke size, trajectory, velocity, route, curvature, inter-stroke time and even the world of the finger every participant used was discovered to be distinctive. For instance, some customers cease utterly when lifting their finger on the finish of a scroll stroke. Others carry whereas the finger continues to be shifting in what the scientists name the “ballistic” scroll.

However behavioral intelligence reaches far past scrolling. Typing rhythms, area navigation, even the imperceptible shifts in how a person holds their cellphone discriminate one person from the following.
The AI Arms Race
Sure behavioral indicators, taken in isolation, might help banks spot apparent fraud. A tool discovered to be the other way up throughout a transaction, for instance, is a serious pink flag. Superhuman typing speeds, impossibly straight cursor actions, or units initiating a transaction whereas in lock display screen mode may also sound the alarm.
Nevertheless, behavioral biometrics programs are way more than rule-based programs. Utilizing linear algebra and statistics, AI fashions can mix extremely nuanced human-computer interface indicators to create user-specific fashions that repeatedly authenticate a person, even after they’ve handed by the point-in-time gateways, like logins or FaceID.
On the AppGate Middle of AI Excellence — the place I work as a machine studying engineer — we practice user-specific behavioral fashions primarily based on cellular phone sensor information. These fashions allow us to supply stay evaluation of whether or not the actions in your machine, or any machine logged into your checking account, are literally you.
Our user-specific anomaly detection fashions, mixed with international, rule-based indicators, assist banks shield towards Account Takeover (ATO) and System Takeover (DTO) assaults. In lots of circumstances, behavioral fashions provide higher safety than conventional biometric markers, similar to fingerprints or facial recognition expertise.
Cyber Provide Chain
The aged are by far the commonest victims of Account Takeover (ATO) or identification fraud. The standard assault is often a multi-step, multi-entity operation, usually beginning with a phishing URL, or social engineering (properly researched psychological manipulation over the cellphone) by which criminals harvest a sufferer’s credentials and promote them to a unique felony group or organizations on huge darkish net marketplaces, such because the infamous Genesis Market, a darkish net discussion board that hosted greater than 80 million credentials stolen from greater than 2 million folks.

These digital fingerprints are exchanged within the market like a typical commodity, and infrequently altering arms a number of instances earlier than reaching the developer or bot that truly makes an attempt to hack into your account. This complicated provide chain makes it a lot tougher for authorities to catch the wrongdoer or culprits as soon as fraud has been reported.
Frequent ATO means criminals bypass the point-in-time authentication (login) from a separate machine, often unknown to the financial institution. Nevertheless, the usual cybersecurity measures utilized by most banks leverage some type of machine intelligence, OTPs, MFA or different machine verification to cease an assault. However new, scarier tendencies are rising the place criminals can render even these strategies out of date.
Rising assault surfaces
At present malware exists that may intercept on-line kinds, remotely log keys as you sort, and even hack straight into your cellphone to intercept MFAs in what known as System Takeover (DTO), ATO’s terrifying cousin. And with the rise of generative AI, the worry that cybercriminals are solely getting began is coming true.
For instance, a deepfake software used within the cybercrime world known as ProKYC permits menace actors to beat two-factor authentication, facial recognition and even stay verification checks utilizing deep pretend movies. A infamous RAT (Distant Entry Trojan) known as BingoMod, distributed by way of smishing (SMS phishing URLs), masquerades as a official anti-virus software in Android telephones, leveraging permissions on the machine that enable a distant menace actor to quietly steal delicate info, similar to credentials and SMS messages, and execute cash transfers originating from inside the contaminated cellphone.
As soon as the machine has been compromised, the entire financial institution’s conventional types of verification are in full management of the attacker. From the financial institution’s perspective, the machine fingerprint is right, the IP deal with is right, MFA codes and authenticator apps all line up. Because of the rise of social engineering, even safety questions, i.e. your mom’s maiden title, present little consolation.
This suggests that the one safeguard towards cybercrime is the authenticity of a particular person’s human conduct.
Steady authentication, fewer interruptions
Rising sophistication in cyberattacks, and in flip extra subtle cybersecurity, has led to 1 constructive consequence for on-line banking prospects: higher person experiences.
Since behavioral fashions can authenticate customers repeatedly, the necessity to continuously ship MFA or OTPs decreases and a official banking session truly goes a lot smoother for purchasers.

The product I at present work on, which known as 360 Danger Management, fuses collectively indicators from bot detection, machine intelligence, desktop behavioral biometrics fashions and cell machine behavioral biometrics right into a single steady danger evaluation evaluation that runs all through each banking session, lengthy after the point-in-time authentication (e.g. login, FaceID).
When danger indicators spike, the system can escalate authentication, request extra verification, and even halt the transaction fully. However when conduct matches the person’s established profile, the session continues seamlessly.
On this manner, behavioral biometrics represents a sea change, from energetic (customers are required to do one thing) to passive (pure conduct turns into the credential), from point-in-time authentication to steady authentication, from fragmented person experiences to intrinsic and protected person workflows.
Additional Studying:
“Touchalytics” – https://arxiv.org/pdf/1207.6231
“ProKYC” – https://www.catonetworks.com/blog/prokyc-selling-deepfake-tool-for-account-fraud-attacks/
“BingoMod” – https://www.cleafy.com/cleafy-labs/bingomod-the-new-android-rat-that-steals-money-and-wipes-data
FBI Web Crime Report – https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf